What Is Digital Identity and How It Works

Digital identity powers a big part of your online life: from logging into banking apps or applying for a mortgage, to proving your age for a restricted site. And what about your phone screen that you unlock with your face? All of these everyday moments rely on one thing – digital identity.
As more services move online, digital identity has truly become a must. This article breaks down what digital identity is, how it works behind the scenes, and why it has become a cornerstone of trust in the digital economy.
What is Digital Identity?
Digital identity is the digital representation of who a person is. It’s made up of verified information, such as your name, date of birth, government-issued ID, biometrics, or device data, that allows you to prove you are who you claim to be online.
In other words, it’s a dynamic profile that includes behavioral biometric data (how you swipe or type), device intelligence (your gadget’s hardware fingerprint), identity wallets (apps storing your credentials securely), and regulations like EU’s eIDAS 2.0.
EXAMPLE: Just like in the physical world, you carry a driver’s license, a credit card, and maybe a gym membership. In the digital world, your identity is a collection of „attributes”, like your name or birthdate, and „credentials”, like a verified token from your government, that prove those attributes are true.
But what’s the main purpose of having a digital ID? By creating a digital ID for identity verification, people get verified quicker! Basically, by being reusable, digital ID minimizes the need to repeatedly provide documents like passports and driver’s licenses to various organizations.
The shift to digital ID aims to create a standardized and secure identity verification system, reducing the reliance on manual checks and paperwork. Digital IDs not only speed up transactions but also eliminate the need to carry physical documents, thus reducing the risk of loss, theft, fraud, and identity theft.
How Digital Identity Works
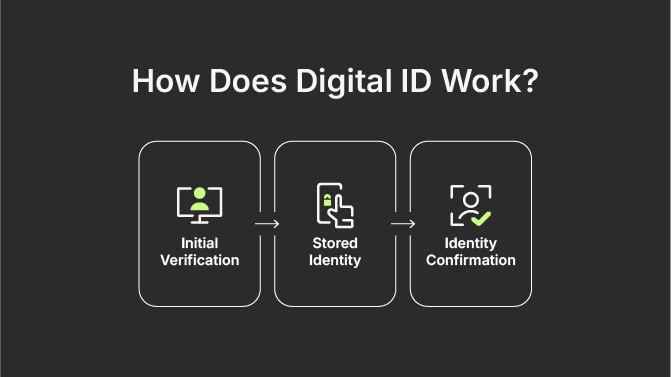
Digital identity verification process consists of three main parts:
- Verification (Onboarding) – the act of proving who you claim to be, during which you provide evidence, like a face scan or an ID document, and the system then checks this information against an „authoritative source”, like a government registry.
- Stored identity (The Wallet) – once verified, your identity is stored securely, often in a Digital Identity Wallet on your smartphone.
- Confirmed identity (Ongoing authentication) – when you need to access a service, you present a credential from your wallet, and the service provider then confirms it’s valid without ever seeing your sensitive raw data.
EXAMPLE: Opening a bank account starts with uploading ID (verification), storing it in an encrypted form (identity vault), then logging in via face scan (confirmation).
There are several core components of digital identity:
- Attributes – individual data points, such as name, age, and/or nationality.
- Credentials – proof that attributes were verified, for example a verified ID.
- Authentication layers – how identity is confirmed later, such as biometrics, passkeys, Multi-Factor Authentication (MFA).
- Trust frameworks – legal and technical standards ensuring reliability, for example eIDAS and NIST certification.
Types of Digital Identities
There are two ways to categorize the types of digital identities.
By Management Architecture – The „How”
This is the most critical distinction for security and privacy. It describes who „owns” the identity data and how it is shared.
Centralized Identity
Each organization, like your bank or an e-commerce site, creates and maintains its own database of users.
- The Experience: You have a separate username and password for every single site.
- The Risk: These are very attractive for hackers. So, if the central database is breached, everyone’s data is exposed.
Federated Identity
This is the „Log in with Google” or „Sign in with Apple” model. One trusted Identity Provider (IdP) vouches for you across many different „Relying Parties” (third-party apps).
- The Experience: You only need to remember one set of credentials.
- The Risk: The IdP becomes a single point of failure. If your Google account is locked or hacked, you lose access to dozens of other services.
Decentralized / Self-Sovereign Identity (SSI)
This is today’s standard. Instead of a central company holding your data, you hold your own verifiable credentials in a digital identity wallet on your phone.
- The Experience: You prove your age or residency by sharing a „cryptographic proof” from your wallet. The company gets the confirmation it needs without ever seeing your actual birthdate or address.
- The Benefit: There is no central database to hack, and you have total control over what you share.
By Entity Type – The “Who”
Digital identity isn’t just for humans anymore; devices and software also need „IDs” to talk to each other securely.
Human Identities
- Workforce identity: Created by your employer to give you access to internal systems (Slack, Email, HR portals).
- Customer identity (CIAM): Created when you sign up for a service as a consumer (Netflix, Amazon).
- Citizen identity: Government-issued IDs like Singapore’s Singpass or the EU Digital Identity Wallet.
Machine and Device Identities
Every laptop, smartphone, and the Internet of Things (IoT) device has a digital identity. This ensures that when your smart thermostat sends data to the cloud, the cloud knows it’s your thermostat and not a malicious hacker.
Service and Cloud Identities
Software applications and „bots” have identities too. This allows one piece of software, for example, an AI agent, to securely access a database without a human having to type in a password every time.
Digital Identity Verification Methods
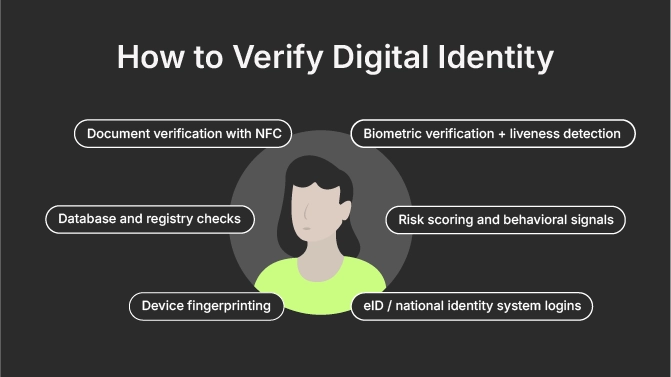
Powered by AI technologies, the number of digital document forgeries is surging, and in 2025 it reached 8 million. So, it’s time to explore the main digital identity verification methods that exist and help us combat identity fraud.
1. Document verification with NFC
Instead of just taking a photo of your passport, you tap it against your phone. Your phone’s Near-Field Communication (NFC) reader „talks” to the chip inside the passport, which is virtually impossible to fake, which adds an extra layer of trust.
NFC offers high assurance levels and is widely accepted; but it requires users to have physical documents and a compatible device on them.
2. Biometric verification + liveness detection
This is the gold standard. The digital identity system captures a 3D map of your face and asks you to blink or turn your head to ensure you aren’t a high-resolution photo or a deepfake, while the iris scanning analyzes the unique color patterns in users’ eyes. At the same time, fingerprint biometrics confirm the person is real and present.
Possible limitations of the biometric data method include lighting issues and some privacy concerns.
3. Database and registry checks
A person’s identity data is cross-checked against trusted sources such as government registries, credit bureaus, sanctions and watchlists. This method is fast, but it depends on data availability, quality, and jurisdiction.
4. Device fingerprinting
This method analyzes device characteristics to detect anomalies or repeated fraud attempts. Tracking 100+ signals like browser settings for unique IDs, it can be persistent over years and spot return visitors.
5. Risk scoring and behavioral signals
This method is a combination of a user’s behavior, device, and transaction context to assess fraud risk in real time. Behind the scenes, systems check if your device „looks” right. Is this the same phone you usually use? Are you typing at a human speed, or is a bot doing the work?
If, for example, an unusual typing speed, or a new device, or a foreign location is detected, then it signals a higher risk score.
6. eID / National identity system logins
Users authenticate via government-backed systems like BankID in the Nordics, Singpass in Singapore, or MitID in Denmark. This method ensures high trust levels of digital identity verification, but it’s limited to the countries that support it with a dedicated technology.
Identity Authentication Methods
At this point, it’s important to clarify the distinction between identification and authentication. Identification means asking the question “Who are you?”, and authentication is about “Can you prove it’s you?”. Put simply: once identity is verified, authentication confirms it repeatedly and securely.
The most common digital identity authentication methods include:
Passwordless authentication uses magic links (secure, one-time-use, time-sensitive URLs sent via email or SMS), OTPs, or biometrics instead of passwords.
Multi-factor authentication (MFA) method combines two or more factors:
- Something you know (PIN)
- Something you have (device)
- Something you are (biometrics)
Biometrics includes facial recognition, fingerprints, or voice recognition to provide frictionless authentication.
Passkeys are cryptographic credentials tied to a device. Meaning they use the security already built into your phone, like FaceID or fingerprint, to log you in, so there’s no password for a hacker to steal.
Continuous authentication signals include behavioral patterns, device consistency, and geolocation signals. This method reduces friction while detecting account takeover attempts early.
The Benefits of Digital Identity
Beyond just being „cool tech”, digital identity systems help solving massive problems for both businesses and users. Here are the most obvious benefits of using digital identity verification.
- Reduced fraud – layered verification and risk analysis stop impersonation and digital identity theft.
- Smoother onboarding – faster sign-ups increase conversion rates.
- Compliance readiness – meets KYC, AML, and data protection requirements.
- Cross-border trust – enables secure access across jurisdictions.
- Improved UX –less friction, fewer repeated checks.
Use Cases of Digital Identity
| Industry | Example |
| Banking | Opening a bank savings account in 2 minutes from home. |
| Travel | Walking through airport security without ever pulling your physical passport out of your bag, by using digital passports and pre-verified traveler identities. |
| Healthcare | Securely accessing your medical history and prescriptions across different hospitals. |
| Gig economy | Verifying that your rideshare driver is exactly who they say they are. |
| Age verification | Proving you are over 18 for a purchase without revealing your exact birthdate or address. |
| eGovernment | Accessing everyday social services (filing taxes, registering for social benefits) and voting online. |
| Remote employment | Verifying new global hires and their rights to work via national IDs. |
Digital Identities Around the World

Mature digital identification systems have transformed governance and services in dozens of countries, with over 280 networks tracked globally covering billions. Leaders like Estonia boast 99% adoption since 2002, enabling 70% of citizens to use it daily for e-voting and contracts, while India’s Aadhaar serves 1.3 billion with 446 million e-KYC checks monthly.
Here’s a list of standout countries with years of proven digital ID success:
Estonia (eID)
eID has been in place since 2002, with 99% of the population using it. PKI-secured cards, combined with Mobile-ID and e-Residency helped 109,000 global users to start businesses remotely. Citizens use it for voting, signing legally binding contracts, accessing health records, and filing taxes. Estonia is currently a lead developer for the EU Digital Identity Wallet, ensuring Estonian IDs work seamlessly across all EU member states.
Denmark (MitID)
Denmark’s NemID was replaced by MitID in 2021, a digital-first system used by over 90% of the population for banking, taxes, and public sector interactions, eliminating the need for physical cards. Seamless for banking and government, MitID has been outpacing its card-heavy EU peers.
Sweden (BankID)
A private-sector, bank-led eID, used since 2003 by nearly 95% of the population for getting access/signatures in health, taxes, and banking sectors. As of January 1, 2026, a new „Authorization System for Electronic Identification” came into force, streamlining how public organizations connect to BankID – to ensure higher security and identity fraud prevention.
The Netherlands (DigiD)
There are two digital identity verification systems used: DigiD for citizens and eHerkenning for businesses. DigiD supports interactions with government entities, while eHerkenning bridges public and private services. DigiD serves 15 million citizens, with eHerkenning handling 13.3 million annual logins.
Germany (eID/Personalausweis)
Germany has a contactless chip-based eID system, embedded in the national ID card, paired with the AusweisApp. Used since 2010 for opening bank accounts, identifying at vending machines, and accessing digital municipal services. The Smart-eID function is stored directly in secure elements of smartphones without needing the physical card for every transaction.
India (Aadhaar)
The world’s largest digital identity system since 2009, represented by a 12-digit unique identity number backed by centralized biometrics (iris/fingerprint). The system is used for „Direct Benefit Transfer” (subsidies), banking (KYC), and mobile SIM activation. As of January 1, 2026, „Face Authentication” has gained full legal recognition, as the system has shifted away from physical photocopies toward QR code-based digital verification to reduce data breaches.
Singapore (Singpass)
The system evolved from 2003 login to app-based biometrics. Managed via a mobile app, Singpass is the centralized digital identity proof for all residents, allowing 5 million users to access 2,700 services. It includes „Myinfo” that auto-fills government forms. Also, it’s integrated with the Assurance Package (AP), allowing the government to disburse cost-of-living payouts directly to bank accounts linked via NRIC/Singpass.
Japan (MyNumber)
Rolled out in the mid-2010s, can now be found in Apple Wallet to support access to taxes and services. In 2026, MyNumber is set to integrate residence/ID cards for foreigners. However, adoption lags due to privacy fears.
Canada (PCTF/DIACC)
An Interoperable framework (not a single ID) certifying private apps like Bluink for legal/banking use, like digital wallets for benefits, health, and finance.
Nigeria (NIMC)
Nigeria’s National Identity Management Commission (NIMC) manages the National Identification Number (NIN) and the Bank Verification Number (BVN). Since 2014, nearly 100 million Nigerians have registered for a NIN, and 58 million have a BVN, despite facing funding and operational challenges.
The Future of Digital Identity: What’s Next?
Here are a handful of predictions that are likely to shape the future of digital identity verification technology:
- Decentralized IDs (DID) will let you control data via blockchain wallets, with no central storage. This means that instead of Facebook or Google „owning” your login, you will own your data.
- You carry your verified credentials on your device in the form of identity wallets, helping you decide who sees what.
- Expect to see more „watermarking” technology, i.e. invisible marks on your digital photos that prevent them from being turned into deepfakes by fraudsters.
- There will be more global interoperability that will allow a UK digital ID to be instantly recognized by a hotel in Tokyo or a bank in New York.
- Digital IDs will be reusable, making it possible to verify your identity once and reuse it everywhere, thus reducing friction and cost.
AI will further improve fraud detection, document analysis, and liveness detection accuracy.
Final Thoughts
Nowadays, almost everything happens online, knowing who’s on the other side of the screen has never mattered more.
And as fraud grows more sophisticated and regulations become stricter, organizations need identity systems that are secure, user-centric, compliant, and future-ready. So, when done right, digital identity protects users, empowers businesses, and offers smooth digital experiences across borders and industries.