What is Multi-Factor Authentication (MFA) and How It Protects Businesses
Did you know that every 39 seconds a cyberattack happens somewhere on the internet? That’s over 2,200 attacks every day! This means that passwords alone can’t protect your business anymore. Phishing emails can trick your employees into disclosing logins, and automated “credential stuffing” attacks attack sites with username-password pairs from previous leaks.
It’s clear as day – the digital threats facing businesses today demand a much stronger defense. One of the solutions is Multi-Factor Authentication (MFA). Having evolved from a nice-to-have security enhancement, MFA is now an essential standard for businesses of all sizes.
In this article, we will explore what multi-factor authentication is, its significance in enhancing digital security, and the benefits it brings to your business.
Multi-factor Authentication Explained

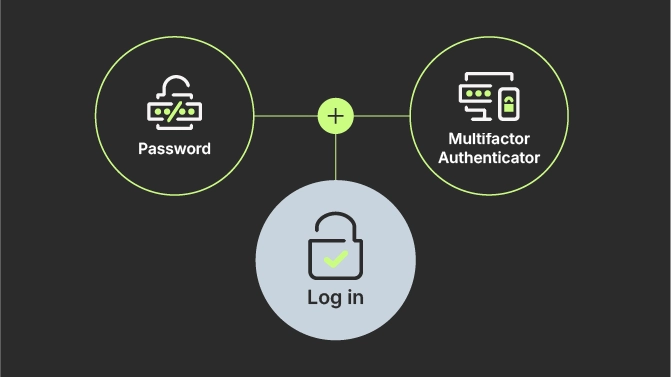
Multi-factor authentication is a security method that requires users to provide two or more verification factors to gain access to a resource: an application, online account, or a VPN. Basically, after entering your password (the first factor), you must provide at least one additional proof of identity, for example, a one-time code on your phone or a fingerprint scan.
And that’s what makes MFA a strong security method: a combination of different types of authentication factors or independent credentials. These factors fall into three main categories:
- Knowledge factor (Something you know): a password, a PIN, or the answer to a security question. It serves as the first line of defense and is often the most familiar form of authentication.
- Possession factor (Something you have): a physical token, an access card, an authenticator device, or a smartphone. These items generate a unique one-time password (OTP) that is time-sensitive and can only be used for a limited period.
- Inherence factor (Something you are): fingerprints, facial recognition, or retinal scan. The biometric authentication method is considered the standard due to its reliability and ease of use.
By requiring factors from different categories, MFA ensures that even if one factor is compromised, unauthorized access is still prevented.
EXAMPLE: A hacker might steal an employee’s password through phishing, but without also stealing the employee’s phone or replicating their fingerprint, the hacker won’t meet the MFA requirements to access the account.
Types of Authentication Factors
Authentication factors are the building blocks of MFA. Let’s break down what each factor type involves, what types of attacks it protects from, and how it contributes to your overall security.
Something You Know (Knowledge Factors)
Knowledge factors are information stored in your memory that only you should know, like passwords and PINs. These symbols you memorized is a way to prove you’re authorized to access an account.
Falling into the same category are security questions, even though they’re less secure than passwords because the answers are often discoverable through social media or public records. Questions like “What street did you grow up on?” or “What was your first pet’s name?” might seem unique and personal, but this information is often surprisingly easy to find.
The main weakness of the knowledge factors is that they can be guessed, phished, or stolen. Once someone learns your password, they can use it just as easily as you can. That’s precisely why relying on passwords alone is no longer sufficient. What you need is additional layers of verification.
Security level: basic.
Something You Have (Possession Factors)
Possession factors require you to have a specific physical object or device to authenticate access. The most common example is your mobile phone, to which you receive a one-time code via SMS, or you enter a code through an authenticator app. So, your phone serves as proof of identity.
Another possession factor are hardware tokens – small devices that generate time-sensitive codes or connect directly to your computer via USB. They’re particularly popular in high-security environments because they’re difficult to remotely compromise.
In the same vein, smart cards, key fobs, and even software certificates stored on specific devices all qualify as possession factors. The underlying principle is simple: if an attacker doesn’t have physical access to your device or token, they can’t complete the multi-factor authentication process, even if they’ve stolen your password.
Security level: medium-high.
Something You Are (Inherence or Biometric Factors)
Inherence or biometric factors use your unique physical characteristics for authentication. The most familiar method is fingerprint scanning. You’ve likely used it to unlock your smartphone or laptop. Today, facial recognition has become commonplace, i.e. using your phone’s camera to verify your identity.
Other biometric factors include iris scanning, voice recognition, and even behavioral biometrics like typing patterns or how you hold your phone. These factors are powerful because they’re inherently tied to you as an individual; you can’t simply hand them over to someone else the way you could share a password.
The appeal of biometrics lies in their convenience and security. You always have your fingerprint with you, you can’t forget it, and it’s extremely difficult for someone else to replicate. However, biometrics aren’t 100% perfect, as they require careful implementation and strong privacy protections.
Security level: high.
Why are Biometric Factors Considered Strong Authentication?
Unlike a password that can be written down or a phone that can be physically taken, your fingerprint or face can’t be easily transferred to an unauthorized person. That’s why biometrics in general stand out among authentication factors: they’re difficult to steal, share, or replicate.
When someone steals your password, they can use it from anywhere in the world. But stealing your biometric data and using it to impersonate you requires sophisticated technology and, often, your physical presence. This complicates things for attackers and makes casual fraud nearly impossible.
Since you can’t share your fingerprint or face, biometric authentication naturally enforces individual accountability.
That said, biometrics aren’t infallible. They require secure implementation to prevent spoofing –using photos to fool facial recognition or fake fingerprints made from lifted prints. To combat this threat, quality biometric systems include liveness detection to verify that what they’re scanning is a real, present human rather than a reproduction.
Privacy is another critical consideration. Biometric data is sensitive and permanent, meaning that you can change a compromised password, but you can’t change your fingerprints. Businesses implementing biometric authentication must ensure this data is encrypted, stored securely, and handled in compliance with privacy regulations like GDPR or CCPA. When implemented thoughtfully with proper safeguards, biometrics provide a robust multi-factor authentication method that balances security with user convenience.
Why MFA is Essential for Business Security

By using multi-factor authentication, businesses can neutralize the most common paths attackers use to breach a network. Here is what MFA can do for your business:
Reduces account takeovers
The primary strength of MFA is its effectiveness against bulk account takeovers. Attackers use stolen credentials from data breaches to access employee accounts, customer databases, financial systems, and sensitive intellectual property.
Microsoft found out that 99.9% of compromised accounts did not have MFA enabled. Luckily, MFA can block nearly all automated bot attacks and phishing schemes by requiring a second authentication factor that attackers simply cannot gain access to.
Neutralizes stolen passwords
Phishing attacks remain a top cause of data breaches, mainly done by tricking employees into revealing their credentials. Also, huge numbers of passwords are available to criminals from past breaches. Fortunately, MFA ensures that a stolen password is not enough to gain entry. So, even if an employee accidentally reveals their credentials, the second barrier stops the incident, preventing a potentially devastating breach.
Protects sensitive data
Today, businesses handle a lot of sensitive information: customer personal data, financial records, intellectual property, etc. Losing or compromising such data is serious trouble. On top of that, credential-based breaches are also very expensive.
A study by IBM revealed that breaches where attackers initially got in with stolen credentials cost companies $4.67 million on average. MFA acts as a financial protection, shielding sensitive customer data and intellectual property by stopping the “chain reaction” that follows an initial compromise, such as accessing confidential data or misusing user accounts to scam others.
Builds user and brand trust
Nowadays, security is a competitive advantage. When customers see that you take authentication seriously, they’re more confident sharing their information with you. A single data breach can destroy years of reputation-building and customer relationships. So, MFA is a visible, tangible investment in protecting the people who trust you with their data.
Ensures compliance and standards
Many regulatory frameworks, such as the Payment Card Industry Data Security Standard rules (PCI DSS), now mandate MFA for administrative access. Additionally, organizations like the US Cybersecurity and Infrastructure Security Agency (CISA) categorize password-only logins as a bad practice. So, implementing MFA demonstrates due diligence to regulators, partners, and insurers.
Protects remote work
Today, a lot of people work remotely in cloud-based business environments. When employees access company resources from home networks, coffee shops, and various devices, the traditional network perimeter disappears. In these circumstances, multi-factor authentication systems provide security that travels with users, protecting access regardless of where they’re connecting from.
To sum up, MFA is now seen as a must-have for business security – a sentiment echoed by cybersecurity leaders as most breaches still trace back to compromised login credentials.
How Does Multi-Factor Authentication Work?
Multi-factor authentication is a fairly straightforward and user-friendly authentication method that can be broken down into two phases: registrationof your MFA factors and authentication during login or transactions.
Registration
When MFA is first enabled, users must enroll their additional factors to “teach” the system how to verify them.
- Users are prompted to configure MFA at their next login or during account creation.
- The user chooses their preferred factor, such as scanning a QR code with an authenticator app, like Google Authenticator, Microsoft Authenticator, Authy, etc., registering a phone number for SMS codes, inserting a hardware security key to link it, or providing a biometric sample, for example: scanning a fingerprint or face if the system supports it.
- To ensure the setup was successful, the system performs a quick test, such as asking the user to enter a code from their new app or phone, or the sensor may ask for multiple scans of your finger.
- The system stores an encrypted representation of the factor; for example, a secret key or biometric template, so it can challenge the user during future logins.
- Users are typically issued one-time recovery codes or asked to register a secondary factor to ensure they aren’t locked out if they lose their primary device. Users might also be encouraged to enroll more than one backup factor; for example, both an authenticator app and a phone number, so they have a fallback.
Authentication
Once registered, the day-to-day login multi-factor authentication process follows a secure sequence:
- The user enters their username and password – “something they know”. If correct, the system moves to the MFA challenge.
- The system requests the second factor, like “Check your app for a code” or “Tap the push notification”.
- The user provides the “something they have” – the code or hardware key – or “something they are” – fingerprint or face scan.
- The MFA system confirms the input matches the stored record. If it doesn’t match or if the request is ignored, access is going to be denied, even if the password was correct.
- Upon successful validation, the user is logged in.
Pro Tip: To keep things more user-friendly, most systems include a “Remember this device” feature, which allows the system to skip the MFA prompt on trusted hardware for a specific period, for example 30 days, unless a high-risk login is detected.
Common MFA Methods Used Today
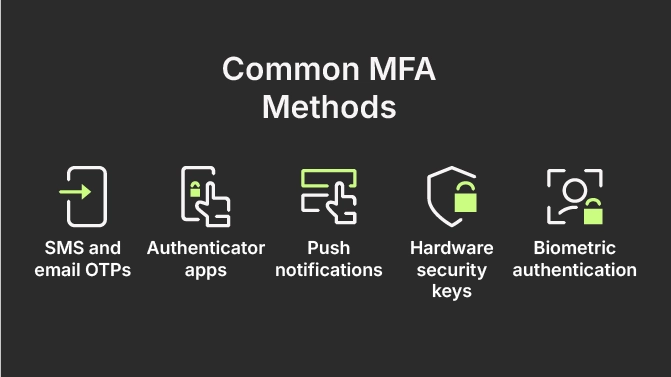
Businesses have multiple MFA options to choose from, each with distinct characteristics, strengths, and limitations. Let’s explore the most common methods currently in use.
SMS and email OTPs
One-time passwords sent via text message or email are among the most accessible and commonly used MFA methods. Users receive a code on their registered phone number or email address, which they enter to complete authentication. Working on virtually any phone, this MFA authentication method doesn’t require special apps or hardware.
However, SMS codes can be intercepted through SIM-swapping attacks or network vulnerabilities, making this one of the weaker MFA options. In fact, the National Institute of Standards and Technology (NIST) restricted SMS-based authentication due to these vulnerabilities, and CISA bluntly recommends against using SMS as a second factor for authentication.
Authenticator apps
Apps like Google Authenticator, Microsoft Authenticator, or Authy generate time-based one-time passwords (TOTPs) directly on your smartphone, which change every 30 seconds and work even without cellular or internet connectivity.
Authenticator apps are more secure than SMS because the codes are generated locally on your device using cryptographic algorithms, making them much harder to intercept. They’re also free and easy to set up, making them an excellent choice for most businesses.
Push notifications
Rather than typing in a code, users receive a notification on their registered device asking them to approve or deny the login attempt. You simply tap “Approve” on your phone when you’re legitimately logging in, or “Deny” if you’re not.
This method is user-friendly and provides additional security because it shows where the login attempt is coming from, helping users identify suspicious activity. However, there’s some risk of “push fatigue”, meaning that users might approve notifications without thinking if they receive too many, potentially approving a malicious attempt.
Hardware security keys
Physical devices connect to your computer via USB, NFC, or Bluetooth to verify your identity. You insert or tap the key when prompted during login, and cryptographic verification happens automatically.
Hardware keys are extremely secure because they’re resistant to phishing, even if you enter your password on a fake website, the key won’t authenticate because it cryptographically verifies the site’s legitimacy. The main drawbacks are cost, because keys must be purchased, and the possibility of physically losing the device.
Biometric authentication
Fingerprint scanners, facial recognition, and other biometric methods are increasingly built into laptops, smartphones, and tablets. They provide seamless authentication: just look at your device or touch the sensor and you’re in. No need to remember codes or carry additional hardware. Although these biometric authentication methods are difficult to steal or share, they too require careful implementation to prevent spoofing and must be handled with appropriate privacy protections.
As you can see – each MFA method represents a trade-off between security, convenience, and cost. The strongest approach often involves offering multiple MFA options and letting users choose what works best for their circumstances while maintaining minimum security standards.
MFA vs. Two-Factor Authentication (2FA)
Often used interchangeably, MFA and 2FA are indeed similar. But not quite, as there’s a technical distinction worth understanding.
As the name suggests, the two-factor authentication (2FA) involves exactly two different authentication factors. Typically, you enter your password and then confirm it with a code from your phone.
Meanwhile, multi-factor authentication (MFA) is the broader term that includes 2FA but also refers to systems requiring three or more factors. A high-security system might require three factors: your password, a code from your authenticator app, and a fingerprint scan. So, that’s MFA, not 2FA.
In practice, most business systems use two factors, making them technically 2FA implementations. The MFA is an umbrella term used in business and security contexts, often regardless of whether the specific implementation uses two, three, or more factors.
The underlying principle is that you use multiple, different types of proof, which significantly strengthens authentication compared to passwords alone. This layered security approach makes unauthorized access significantly harder.
The Pros and Cons of MFA
To help you implement MFA effectively and set appropriate expectations, let’s compare the benefits and challenges behind multi-factor authentication as a security measure.
Pros
Stronger security
The most obvious and biggest pro – MFA improves account security. By requiring multiple independent factors, MFA authentication methods prevent unauthorized access even if passwords are leaked or guessed.
Reduced fraud
When MFA is on, account takeovers, fraudulent transactions, and unauthorized access become much more difficult. Even sophisticated phishing attacks typically only capture passwords, leaving attackers unable to complete authentication. This protects both your business and your customers from fraud-related losses that would otherwise cost millions.
Compliance support
Many regulatory frameworks and industry standards now expect or require MFA. Implementing it helps you meet compliance obligations for standards like SOC 2, PCI DSS, HIPAA, and others. This isn’t just about checking boxes. It demonstrates due diligence in protecting sensitive data and can be crucial during audits or in the aftermath of security incidents.
Improved trust
Customers are increasingly aware of two-factor authentication, as many use it for personal email, banking, social media. So, when customers and partners see that you’ve implemented strong authentication, it signals that you take cyber security seriously. The use of MFA builds confidence in your organization’s ability to protect its data and can be a competitive differentiator, particularly in industries where data protection is a primary concern.
Flexibility and scalability
MFA solutions scale from small businesses to global enterprises. Cloud-based MFA services make implementation accessible without requiring significant infrastructure investment, and you can adjust protection levels based on risk, requiring stronger authentication for administrative accounts or sensitive systems while using simpler methods for lower-risk access.
Cons
User friction
The most common complaint about MFA is that it adds extra steps to the login process. Users must have their phone accessible, wait for codes, or complete biometric scans. While these steps typically take only seconds, they represent additional effort compared to just typing a password, which often leads to user resistance, particularly during initial rollout.
A survey of IT professionals found that 67% agreed that adding extra security measures like MFA makes the user experience more cumbersome. Source
Implementation costs
While many MFA solutions are affordable or even free, there are costs involved in deployment, training, ongoing support, and potentially hardware tokens for employees who need them. For large organizations, these costs can be significant, though they’re typically far less than the cost of a single data breach.
Device/technology dependency
Most MFA methods require users to have a smartphone or other device. If someone’s phone battery dies, they lose their device, or they’re in an area without service, they might be unable to authenticate. If a hardware token is lost or left at home, that user might be stuck until IT can bypass MFA for them. This creates potential disruptions that businesses must plan for through backup authentication methods and account recovery procedures.
Recovery challenges
In a password-only world, if you forgot your password, you hit “Reset password” and go through email verification. In an MFA world, when employees lose access to their authentication factors: lose a phone, break a hardware key, or get locked out, IT teams need secure processes to restore access without compromising security. Users should be educated to set up a backup ahead of time. But if they don’t, support must step in, which increases operational load.
Not completely foolproof
MFA is not invincible, as attackers are adapting and coming up with more sophisticated plots, like phishing toolkits now that can intercept OTP codes in real-time via proxy websites. Also, there have been incidents of MFA fatigue attacks, where users accidentally approve fraudulent login prompts out of confusion or annoyance. So, implementing MFA shouldn’t lead to complacency about other security practices, it’s just one layer in a comprehensive security strategy, not a complete solution on its own.
The table below sums up all the benefits and the trade-offs of multi-factor authentication.
| Feature | PROS | CONS |
| Security level | High-level protection: Blocks 99%+ of automated attacks and routine phishing. | Not invincible: Advanced threats, like MFA fatigue or proxy attacks, still exist. |
| Financial impact | Financial safeguard: Prevents takeovers that cost an average of $4.67M per breach. | Operational overhead: Requires initial setup time, subscription fees, or hardware costs. |
| User experience | Enhanced trust: 86% of users feel safer; signals you value data privacy. | Added friction: Extra steps can frustrate users and increase helpdesk tickets. |
| Compliance | Regulatory ease: Meets insurance requirements and industry mandates (PCI DSS, CISA). | Recovery complexity: Managing lost devices requires a secure (and often manual) reset process. |
| Reliability | High ROI: Low-cost insurance compared to the catastrophic cost of a breach. | Hardware reliance: Productivity stops if a phone dies or a security key is left at home. |
MFA Implementation Best Practices
To effectively implement MFA and better balance security and usability, it’s a good idea to be aware of the best practices.
1. Match factors to risk
Not all accounts need the same level of protection. Evaluate your users’ needs and the sensitivity of the data they access.
- High risk: Mandate hardware security keys or biometrics for admins.
- Standard risk: Use authenticator apps or push notifications for daily tasks.
- Flexibility: Offer a variety of options to accommodate users without smart devices.
2. Move beyond SMS-based MFA
While better than nothing, SMS and email codes are vulnerable to SIM swapping and interception.
- Use authenticator apps or FIDO2/WebAuthn security keys for critical systems to prioritize security
- Avoids default procedures and don’t rely on SMS for high-value administrative access.
3. Prioritize user experience
To prevent users from seeking workarounds, make MFA as seamless as possible:
- To reduce friction, implement Single Sign-On (SSO) and “remember this device”.
- Use risk-based MFA to only prompt for a code during unusual login attempts.
- Explain to users that MFA is a “second lock” protecting their personal data.
4. Provide backup and recovery
Plan for lost phones or broken tokens to avoid productivity stalls:
- Provide one-time-use recovery (backup) codes.
- Encourage users to register an alternate email or phone number.
- Establish a strict identity-verification process for MFA resets.
5. Review and audit regularly
Over time, your business environment might change, and so do threats. That’s why it’s important to periodically audit who in your organization has MFA enabled and for which systems:
- Ensure new apps are integrated and revoke access for departing employees.
- Review failed attempts and bypass requests to identify potential attacks or user friction.
- Stay current on phishing-resistant technologies and phase out deprecated methods.
6. Educate your team
Human factors are crucial for adoption. Provide clear setup instructions and run awareness campaigns. When users understand the “why”, they become partners in your security culture rather than obstacles to it.
7. Test your implementation
Before rolling out MFA organization-wide, pilot it with a smaller group to identify issues, gather feedback, and refine your approach.
- Test account recovery procedures to ensure they work smoothly when employees need them.
- Conduct tabletop exercises where you simulate an employee losing their phone or other scenarios to verify your processes are practical and secure.
Final Thoughts: MFA’s Application and Future
What makes MFA particularly powerful is its scalability and accessibility. Whether you’re a solo entrepreneur or running an enterprise, cloud-based MFA solutions fit virtually any budget and technical capability. The upfront effort of deployment pays ongoing dividends in reduced risk, regulatory compliance, and customer trust.
Looking ahead, expect MFA to evolve beyond traditional methods. Passwordless authentication using biometrics and security keys is gaining momentum, adaptive authentication will become smarter at balancing security with user experience, and regulatory pressure will continue making MFA a requirement across more industries.